 ‘Once men turned their thinking over to machines in the hope that this would set them free. But that only permitted other men with machines to enslave them.’ — Frank Herbert (1920-1986), in ‘Dune’
‘Once men turned their thinking over to machines in the hope that this would set them free. But that only permitted other men with machines to enslave them.’ — Frank Herbert (1920-1986), in ‘Dune’
By sheer cowinkydink, another ransomware attack has taken down operations of another major American industry. This time, the target is America’s largest meat processer, JBS.
White House Deputy Press Secretary Karine Jean-Pierre on Tuesday said that the hacker group behind the attack is “likely based in Russia.”
Wednesday morning, in another of a series of whodathunk moments, the FBI issued a statement revealing that Russian-linked hackers “REvil and Sodinokibi” are behind the ransomware attack on JBS meat processing facilities.
JBS acquired a fake, plant-based meat company for $500 million, and its CEO has been using Joe Biden’s “build back better” slogan and other World Economic Forum and United Nations jargon. It has moved into the faux-burger market in Europe.
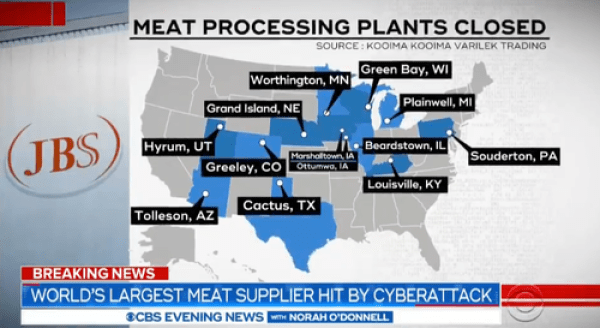
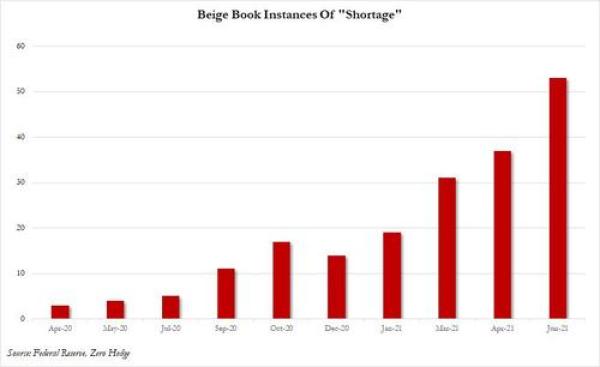
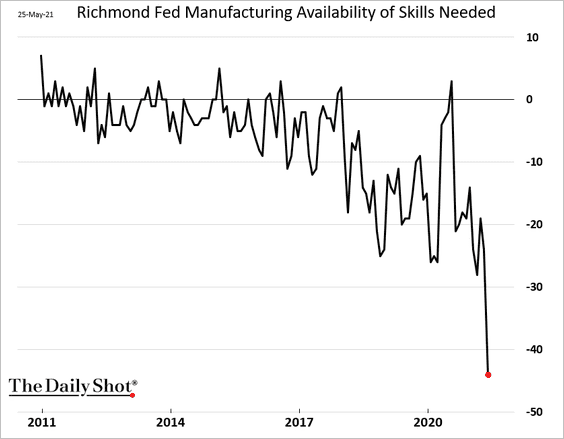
First, it was Texas energy, then the Colonial gas pipeline and now meat. All of this is happening as shortages are commonplace, caused by massive economic distortions from lockdowns, money printing crack up boom and “stimulus,” and putting people on permanent unemployment largesse. Is this a distraction to justify the rise in prices (aka inflation)?
As another precursor to yet another drill going live — namely, the July 9, 2021, Cyber Polygon cyberattack “exercise” simulations — we learn that overnight downdector users reported AT&T service across the Baltimore–Washington metropolitan area experienced widespread outages.
About the same time, Apple reported problems with the functioning of its Apple Card credit card and payment system that was affecting all users.
The Cyber Polygon exercise will focus on simulating the downing of the global internet, as well as disruptions to power supplies and control grids.
That’s right. In July, the summer month for peak heat in most of North America, there will be forced power outages.
What will happen when the air conditioning goes out while temperatures hover around 100 F in America’s largest cities?
The final spark for the long, hot, summer conflagration will be when Darren Chauvin is exonerated on a technicality.
And it’s not exactly like a warning hasn’t been issued by the Wizard of Oz, Mr. Diabolica himself, Klaus Schwab. He announced at the last World Economic Forum gathering that the coming “cyber pandemic will make COVID-19 look like a non-event.”
Anyone beginning to see a pattern?
Meat packers and gas pipelines can be hacked but not elections? Thanks, comrade.
Any company big enough to be a cyberattack target is big enough to design work-arounds.
They never attack Beyond Meat, Woka-Cola or Proctor & Gamble, do they? How odd. Somehow Tesla doesn’t have any semi-chip shortages. You won’t see a solar panel company “hacked” or a vaccine company.
Watch for more “attacks” on anything and everything that supports self-sufficient, regional or middle class economies, such as the hack that nearly poisoned the water supply of Oldsmar, Florida, in February.
Part of Agenda 21 is to reduce meat consumption — not for those at the top of the pecking order, just for the “commoner” plebs. It’s also engineered to remove humans from normal processes so that they can be laid off and the Crime Syndicate minions running the corporations still get a big bonus.
Of course, this is great for the shareholders until the day the automation breaks “Dune”-style, and then everything collapses because no one knows how to fix anything manually any more.
We’ve seen how easy it is to scare people with a flu that rarely kills old fat already ill people. Just think how scared and aggressive people will be with no gas in their tank or no food on their table, or in sweltering heat without air conditioning. You think Popeyes chicken shacks are dangerous now, just wait.
Shock the system and test the results. First an energy shock, then an oil shock, now a food shock; and, yes, they probably have a money shock planned for the future.
So, time to go with the nice, safe, government-backed, digital dollar? The best way to deploy it is to get people clamoring for it.
They will use this to disable access to “unsafe” dissident sites, just as Cass Sunstein and his ilk recommended.
This is a fifth-generation world war being run by a global Crime Syndicate, and the enemy is any and all competition. They use alarmist imperatives as a cover for yet more greed, corruption, enslavement and to feed their lust for power and control.
Read the full article at Winter Watch.
UPDATE:
Since publishing this earlier today, ZeroHedge News is reporting about another Cyberattack on the Massachusetts ferry system.
The Hacks Keep On Comin’: Mass. Ferry Service Suffers Cyberattack; New York’s MTA Admits April Breach
In what is certain to be a recurring theme that has already been thrust into prominence with recent ransomware hacks of the Colonial Pipeline and JBS, the world’s largest meat producer, cybercriminals struck yet another target on Wednesday: the US state of Massachusetts ferry system. Additionally, the MTA admitted this week that it was the target of an April attack.
Service between several upscale northeastern coastal communities was disrupted as a result of the ferry system attack, according to AFP. The attack was reported by The Steamship Authority of Massachusetts, which offers ferry service between Cape Cod, Nantucket and Martha’s Vineyard.
The Authority tweeted out: “There is no impact to the safety of vessel operations, as the issue does not affect radar or GPS functionality.”‘
However, the hack did hit the Authority where it could arguably hurt worse: its payment system. The ferry was temporary limited to cash (gasp) after it lost its ability to process credit cards. On Facebook, the Authority wrote that it was “…unable to release or confirm specific details of what occurred,” but that it was working with local, state, and federal officials to figure out the incident.
In keeping with the theme of mass transit, the Metropolitan Transportation Authority (MTA) revealed on Wednesday that it was also hacked on April 20.
The group believed to be responsible for the MTA hack is said to have links to the Chinese government, the NY Times reported Wednesday. A follow up audit after the attack revealed “no signs that the operating systems had been affected, or that the hackers accessed information of clients or employees”.
“The hackers did not gain access to systems that control train cars and rider safety was not at risk,” transit officials said, according to the NY Times. However, there was residual concern that these systems could be breached through a back door, according to MTA documents.
“The attack on the M.T.A. did not involve financial demands and instead appears to be part of a recent series of widespread intrusions by sophisticated hackers believed to be backed by the Chinese government,” the Times wrote. The MTA was one target out of a group of “dozens” of federal agencies, the report notes.
Rafail Portnoy, the M.T.A.’s chief technology officer, said: “The M.T.A.’s existing multilayered security systems worked as designed, preventing spread of the attack. We continue to strengthen these comprehensive systems and remain vigilant as cyberattacks are a growing global threat.”
But the growing theme not only of targeting mass transit – but also of ransomware attacks in general – are both worth keeping a close eye on, as these feel like anything but isolated incidents.
**By Tyler Durden
**Source
